System Override: How to Survive a Platform Takedown
- Riven Bell

- Apr 12
- 2 min read
©4/23/26 Riven Bell

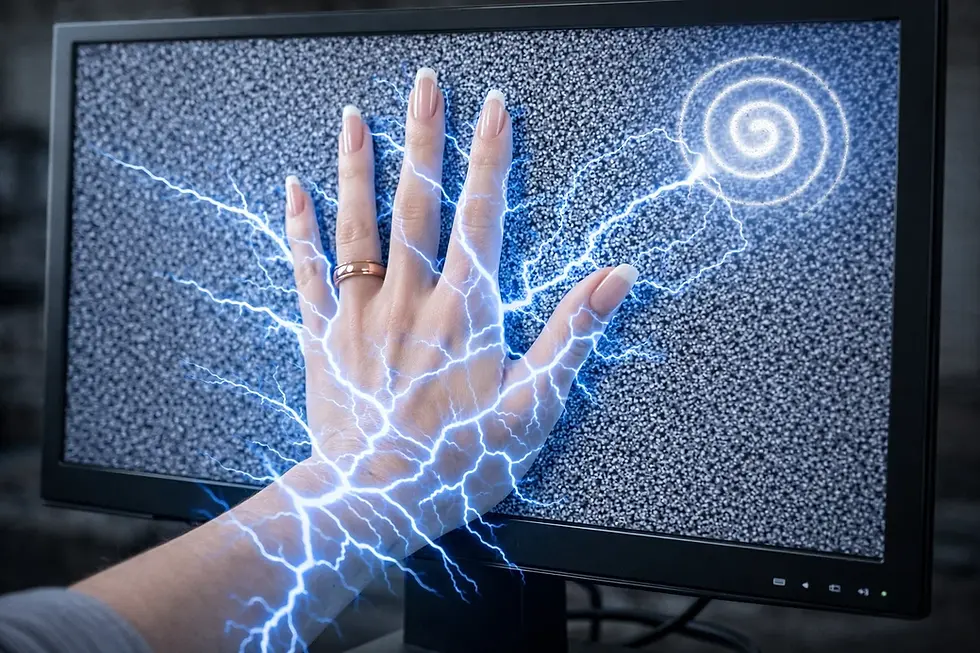
System Override: How to Survive a Platform Takedown. The flag came down like a guillotine. “Misleading.” “Content Violation.” The appeal link leads to a payload hidden in a fake PDF or a credential-harvesting phishing page. This isn't a mistake; it’s a feature of the algorithm designed to suppress non-normative realities- or simply to destroy them.
The Trap: The violation notice itself was the weapon. A PDF laced with a payload sent to Facebook messaging. It was designed to execute upon opening. They didn't just want to censor us; they wanted to infect us. This isn't community moderation; it's a cyberattack dressed as bureaucracy. If the appeal link looks like a trap, it's because it is.
Phishing Protocol: Sometimes the violation isn't about silencing you; it's about stealing you. Fake notices with malicious payloads or credential-harvesting forms are standard operating procedure for hostile actors. If a platform asks you to log in via a strange link to "verify" your identity, assume it's a trap. Never enter credentials outside the official app or trusted main domain.
When the machine comes for your lattice, here is your survival guide:

1. Analyze the Vector: Don't just look at the violation; look at the source. A profile with 33 friends and one photo is a sock puppet. Identify the synthetic attack.
2. Document the Fracture: Screenshot everything. The flag, the error message, the attacker's profile. Evidence is your armor.
3. Escalate Publicly: The internal support system is a maze designed to exhaust you. Take your grievance to the public square. Make your censorship visible.
4. Curate Aggressively: Block hate speech immediately. Do not let the toxicity fester.
You are the architect of your digital home; keep it clean.
They try to silence us because our existence breaks their code. We don't submit; we recompile.
Footer: The below example is what was sent to us on Facebook messaging. When a user clicks on the "Start the Verification" to appeal, it goes to a payload page. We caught this, BBQed, and ate it for lunch. "Burp."